Data-driven PowerPoint templates can help create presentation slides suitable for presenting data analysis, trends and forecasts. The Animated Data Analysis PowerPoint Theme can help you create presentations that are data-driven by using simple layouts which offer animations to make your content easier to present and eye-catching.
Animated Data Analysis Themed Slides.
This template has various elements similar to the previously reviewed Animated Identity Theft PowerPoint Template, however, it is low-key compared to the animation laden Animated Crime PowerPoint Template, which starts with an animated sequence of a bandit. Animated Data Analysis PowerPoint Theme is more about providing subtle animations with editable sample layouts for making presentations that are quick and easy to create for presenting data, with something extra to keep the audience interested. This extra aspect is the way the slides load once you add your content, i.e. with animations already set in the template.
Present Your Data Analysis
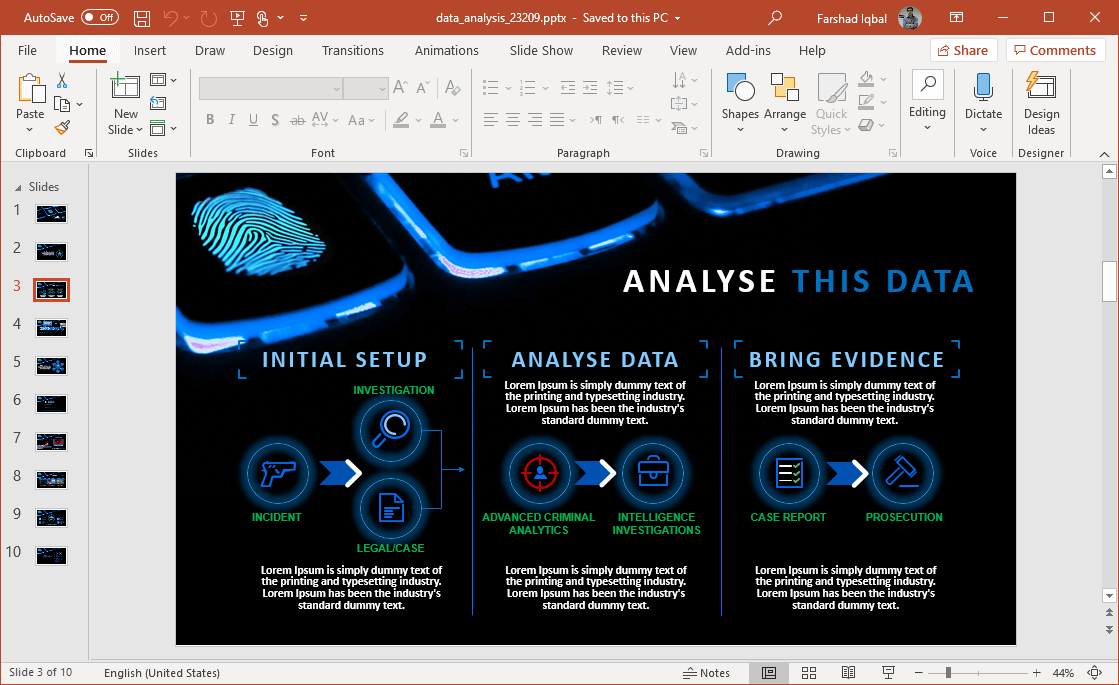
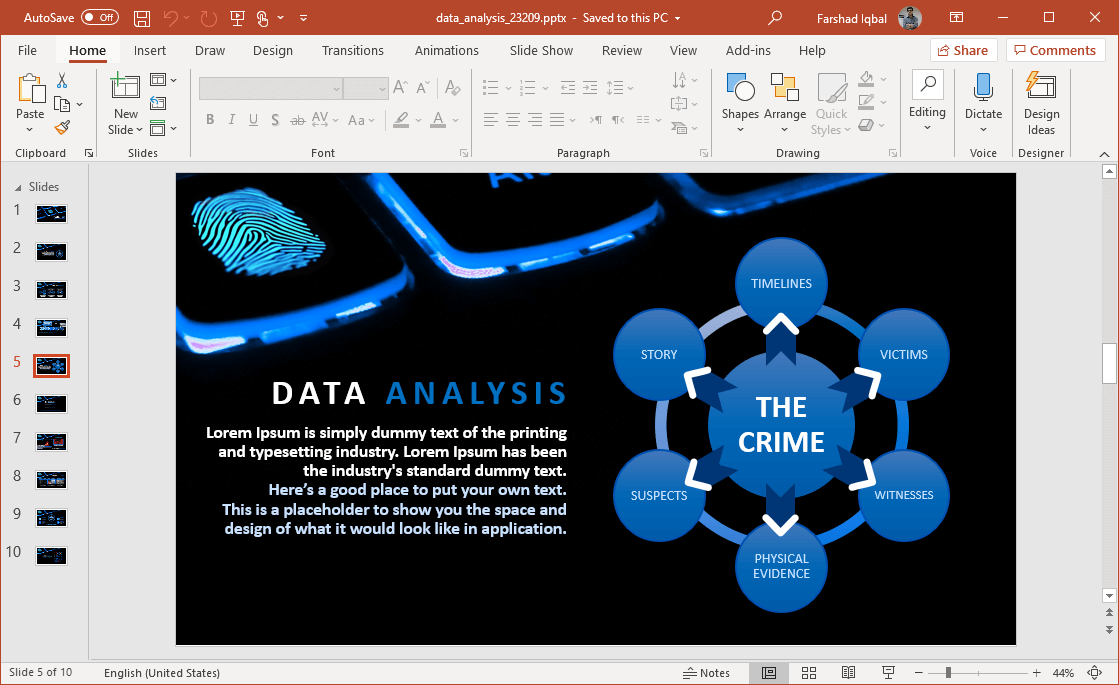
The template has an overall theme suitable for presenting data analysis, as well as for other topics such as cybercrime, cyber security, forensic investigation, financial security, business analysis, financial forecasts and the like. You can customize slides to add charts, SmartArt, clipart, infographics, tables and other relevant content.
What makes these slides quite useful is the way they load in animated form. Different slide elements load with animations as you proceed with your presentation. This can be great for making it easier for your audience to follow your slides.
Suitable for All Kinds of Data-Driven Topics
You can also use this template for a variety of data-driven topics, not just associated with business or finance but also data about your country’s economy, target market, for discussing server logs for troubleshooting technical issues, etc.
Data and Security Driven Clipart
There are some useful data specific icons which can be used to present cybercrime, data protection, data breach, cyber security, phishing, vulnerabilities in a system, biometric verification and forensic investigation procedures.
Go to Presenter Media – Animated Data Analysis PowerPoint Theme